Last revision (mm/dd/yy): 09/11/2017
- Owasp Cheat Sheet Pdf
- Owasp Sql Injection Prevention Cheat Sheet Download
- Owasp Sql Injection Prevention Cheat Sheet Free
- Owasp Stored Procedures
- The code has to be injected in such a way that the SQL statement should generate a valid result upon execution. If the executed SQL query has errors in the syntax, it won't featch a valid result. So filling in random SQL commands and submitting the form will not always result in succesfull authentication.
- You can find more on this topic on the OWASP prevention Cheat Sheet. SQL injection common filters bypass. To prevent SQL injection, developers use common filters to check user input. Unfortunately, they can be bypassed. Whether you are As a developer or an ethical hacker, you should be aware of them.
- SQL Injection Prevention Cheat Sheet; JPA Symptom. Injection of this type occur when the application use untrusted user input to build a JPA query using a String and execute it. It's quite similar to SQL injection but here the altered language is not SQL but JPA QL. Use Java Persistence Query Language Query Parameterization in order to prevent injection.
SQL Injection Prevention Cheat Sheet from OWASP. Saved by Aquilino Arts.
- 2Parameterized Query Examples
SQL Injection is one of the most dangerous web vulnerabilities. So much so that it's the #1 item in the OWASP Top 10. It represents a serious threat because SQL Injection allows evil attacker code to change the structure of a web application's SQL statement in a way that can steal data, modify data, or potentially facilitate command injection to the underlying OS. This cheat sheet is a derivative work of the SQL Injection Prevention Cheat Sheet.
Owasp Cheat Sheet Pdf
SQL Injection is best prevented through the use of parameterized queries. The following chart demonstrates, with real-world code samples, how to build parameterized queries in most of the common web languages. The purpose of these code samples is to demonstrate to the web developer how to avoid SQL Injection when building database queries within a web application.
Prepared Statement Examples
Owasp Sql Injection Prevention Cheat Sheet Download
| Language - Library | Parameterized Query |
|---|---|
| Java - Standard | |
| Java - Hibernate | |
| .NET/C# | |
| ASP.NET | |
| Ruby - ActiveRecord | |
| Ruby | |
| PHP - PDO | |
| Cold Fusion | |
| Perl - DBI |
Stored Procedure Examples
The SQL you write in your web application isn't the only place that SQL injection vulnerabilities can be introduced. If you are using Stored Procedures, and you are dynamically constructing SQL inside them, you can also introduce SQL injection vulnerabilities. To ensure this dynamic SQL is secure, you can parameterize this dynamic SQL too using bind variables. Here are some examples of using bind variables in stored procedures in different databases:
| Language - Library | Parameterized Query |
|---|---|
| Oracle - PL/SQL | Normal Stored Procedure - no dynamic SQL being created. Parameters passed in to stored procedures are naturally bound to their location within the query without anything special being required. |
| Oracle - PL/SQL | Stored Procedure Using Bind Variables in SQL Run with EXECUTE. Bind variables are used to tell the database that the inputs to this dynamic SQL are 'data' and not possibly code. |
| SQL Server- Transact-SQL | Normal Stored Procedure - no dynamic SQL being created. Parameters passed in to stored procedures are naturally bound to their location within the query without anything special being required. |
| SQL Server- Transact-SQL | Stored Procedure Using Bind Variables in SQL Run with EXEC. Bind variables are used to tell the database that the inputs to this dynamic SQL are 'data' and not possibly code. |
Owasp Sql Injection Prevention Cheat Sheet Free
- OWASP SQL Injection Prevention Cheat Sheet
Owasp Stored Procedures

Learn or teach how to code with best-of-industry tools from JetBrains. Free Educational Licenses for JetBrains' tools. All of the functionality of our lightweight IDEs can be found within IntelliJ IDEA (you need to install the corresponding plug-ins from the repository). It includes support for all technologies developed for our more specific products such as Web/PhpStorm, RubyMine and PyCharm. IntelliJ IDEA vs PhpStorm vs WebStorm: What are the differences? The major difference between these three IDEs (Integrated Development Environments) is the language each supports. IntelliJ IDEA is a Java IDE. PhpStorm is a PHP IDE, and WebStorm is a JavaScript IDE. The following features are available for free with IntelliJ IDEA Community Edition. 20 006 642 downloads. Rust language support. 2 694 603 downloads. PhpStorm Web Help for offline use. 23 978 downloads. Top Rated for IntelliJ. PhpStorm is a PHP IDE which keeps up with latest PHP & web languages trends, integrates a variety of modern tools, and brings even more extensibility with support for major PHP frameworks. IntelliJ IDEA and PhpStorm can be primarily classified as 'Integrated Development Environment' tools. Some of the features offered by IntelliJ IDEA are. 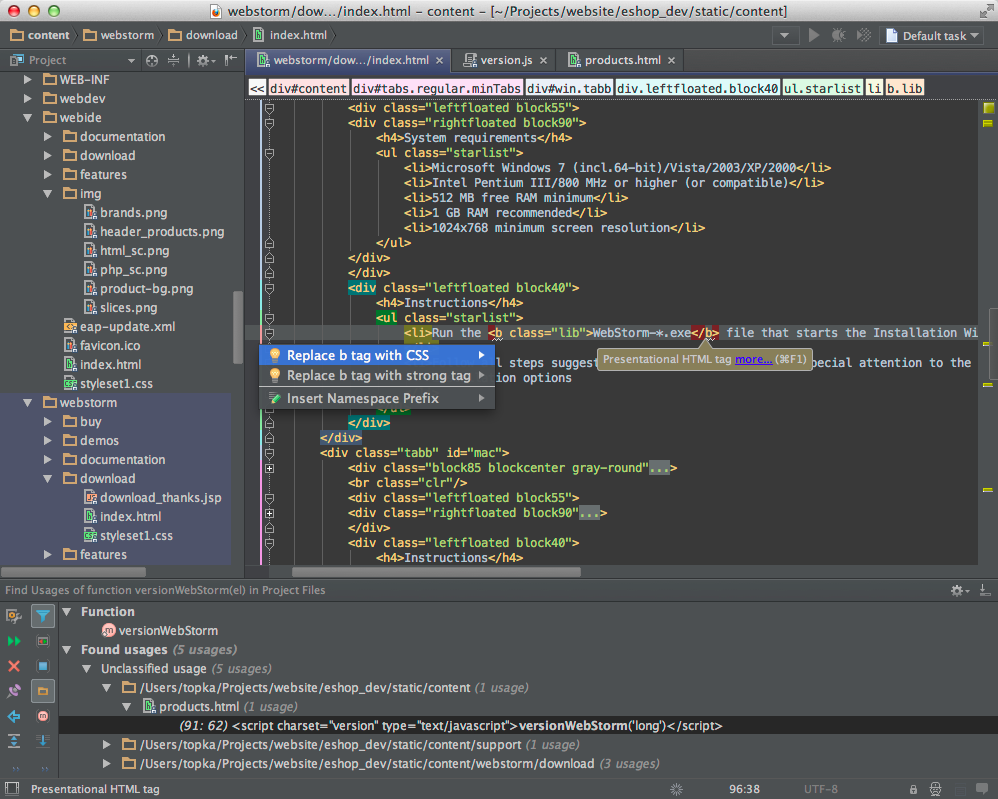
Jim Manico - jim [at] owasp.org
Dave Wichers - dave.wichers [at] owasp.org
Neil Matatal - neil [at] owasp.org
